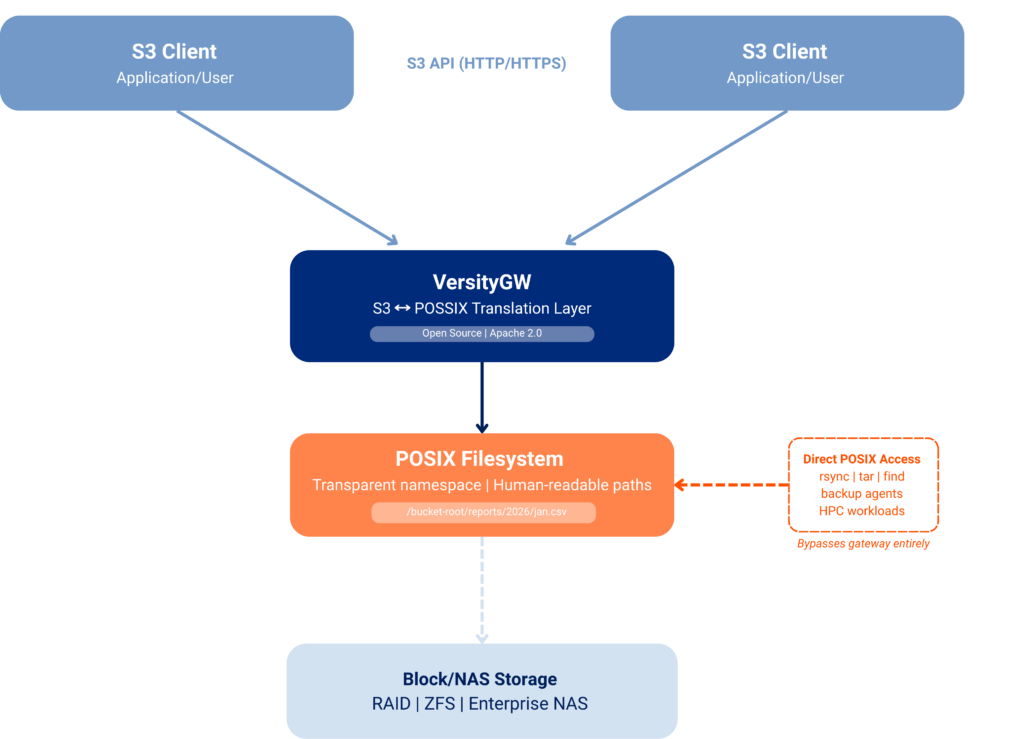
The Versity S3 Gateway‘s POSIX backend stores S3 objects as ordinary files at predictable, human-readable paths — giving administrators direct access to their data through standard POSIX tools without gateway involvement. Unlike purpose-built object stores that lock data behind a proprietary interface, the Versity S3 Gateway layers S3 compatibility over a namespace that admins can inspect, manage, and protect using the tools they already know. Durability comes from the underlying storage system — RAID, ZFS, or enterprise NAS — rather than requiring erasure coding within the gateway itself.
One of the defining design decisions in the Versity S3 Gateway’s POSIX backend is its approach to object storage. Rather than storing objects in an opaque, gateway-specific format, VersityGW translates S3 object keys directly into filesystem paths. An object stored as reports/2026/january.csv in a bucket becomes exactly that relative path on the POSIX filesystem — no encoding, no indirection, no proprietary layout.
This transparency has meaningful implications for administrators who need to maintain control over their data beyond what the S3 API alone provides.
Direct Path Mapping
When a client uploads an object through the S3 API, VersityGW creates the corresponding directory hierarchy and file on the POSIX backend verbatim. The mapping is straightforward:
|
S3 Object Key
|
POSIX Path (relative to bucket root)
|
|
file.txt
|
file.txt
|
|
logs/app/2026-03-01.log
|
logs/app/2026-03-01.log
|
|
backups/db/snapshot.tar.gz
|
backups/db/snapshot.tar.gz
|
This means that anyone with POSIX access to the storage system can browse, read, and manage the data using familiar tools — ls, find, rsync, cp, and so on — without any knowledge of the gateway or its configuration.
Access Paths to Data
The S3 API is one path to the data — not the only one. Administrators and applications can reach the same namespace directly via POSIX.
Access S3 Data Without the Gateway
The S3 API is one path to the data, but not the only one. Because files exist at predictable, human-readable paths, any application that can access the underlying filesystem can work with the data directly.
Backup utilities such as rsync, tar, or enterprise backup agents can back up and restore data without needing S3 API support or gateway involvement. Monitoring tools, log collectors, virus scanners, and archival pipelines can all operate on the primary namespace without modification.
This eliminates a common problem with purpose-built object stores, where data is only reachable through a single proprietary interface. With the Versity S3 Gateway’s POSIX backend, that constraint disappears.
Example: A nightly rsync job backing up /mnt/bucket-root/reports/ requires no knowledge of VersityGW. It sees ordinary files and directories — because that’s exactly what they are.
A Familiar Namespace for Storage Administrators
Administrators accustomed to POSIX environments can apply their existing knowledge directly. Meatadata can be inspected with ls, and files can be located with find. There is no need to translate between an object key and an internal identifier to perform routine maintenance or investigation.
Background tasks such as custom retention scripts, compliance exports, or integration with HPC workloads can be implemented directly against the POSIX namespace without requiring S3 API calls or gateway coordination.
Example: To find all log files older than 30 days across all buckets, an admin can run:
find /mnt/bucket-root -name "*.log" -mtime +30
No S3 API calls, no gateway coordination, no specialized tooling required.
No Vendor Lock-in at the Data Layer
Because VersityGW stores data as ordinary files, migration away from or alongside the gateway requires no data transformation. The files are simply files. If the gateway is decommissioned or replaced, the data remains intact and immediately accessible to whatever replaces it — a meaningful advantage over proprietary object stores that require export tooling or vendor assistance to retrieve data.
The primary trade-off of this direct mapping approach is that objects stored on a POSIX backend are not erasure-encoded the way data is in many purpose-built distributed object stores. A single file represents a single copy of an object.
However, this does not mean the data is unprotected. The POSIX backend is intended to be deployed on storage systems that provide their own redundancy at the block or filesystem level:
- Hardware RAID (e.g., RAID 5, RAID 6, RAID 10) provides device-level fault tolerance with no changes to the filesystem or gateway.
- Software RAID via
mdadm, lvm, or similar tools offers comparable protection without dedicated hardware.
- ZFS provides built-in data integrity checksumming, mirrored and RAIDZ vdevs, and automatic self-healing. See this ZFS Use Case for a detailed discussion of deploying VersityGW on ZFS.
- Enterprise NAS or SAN systems with their own redundancy, snapshotting, and replication features can serve as the backend while the gateway presents the S3 interface to clients.
- Filesystem Snapshots (Btrfs, ZFS, or NAS) provide point-in-time recovery without requiring any S3-level versioning configuration.
- POSIX-level replication tools (
rsync, rclone, zfs send, etc) can maintain offsite or secondary copies independently of the gateway.
Block- and filesystem-level redundancy replaces erasure coding, and the choice of underlying storage determines the durability characteristics of the deployment.
For organizations evaluating S3-compatible gateways, the POSIX transparency of VersityGW represents a meaningful architectural difference. Data stored through the Versity S3 Gateway is accessible via standard tools, portable across storage systems, and free from the single-interface dependency that characterizes many competing solutions.
If you’re comparing S3 gateway options or planning a deployment on POSIX-compatible storage, explore the full VersityGW documentation or contact the Versity team to discuss your use case.